Jibi MosesMarch 24, 2026
Jibi MosesMarch 24, 2026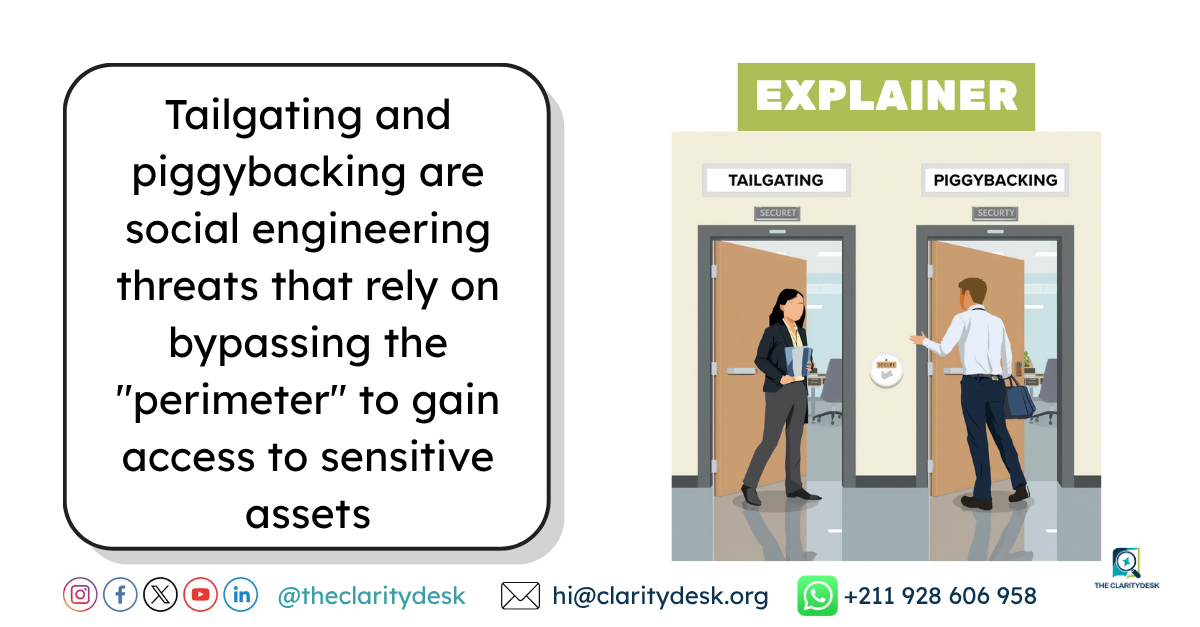
| Feature | Tailgating | Piggybacking |
| Awareness | The authorized person is usually unaware. | The authorized person is fully aware. |
| Method | Stealth and timing (sneaking in). | Manipulation of social norms/politeness. |
| Interaction | No direct interaction required. | Requires a level of trust or social engineering. |
| Intent | Purely deceptive. | Can involve a “friendly” accomplice or a tricked employee. |